Managing IoT Device Vulnerabilities in Fleets
Michael Bar

IoT devices play a key role in fleet management, providing real-time data on vehicle locations, driver behaviour, and performance. However, this connectivity comes with serious risks. Cyberattacks targeting IoT devices in fleets have surged, with incidents like the 2024 breach of a UK telematics provider exposing 70TB of sensitive data. Weak encryption, poor authentication, and outdated firmware are common vulnerabilities that attackers exploit, leading to disruptions, data theft, and compliance issues under GDPR.
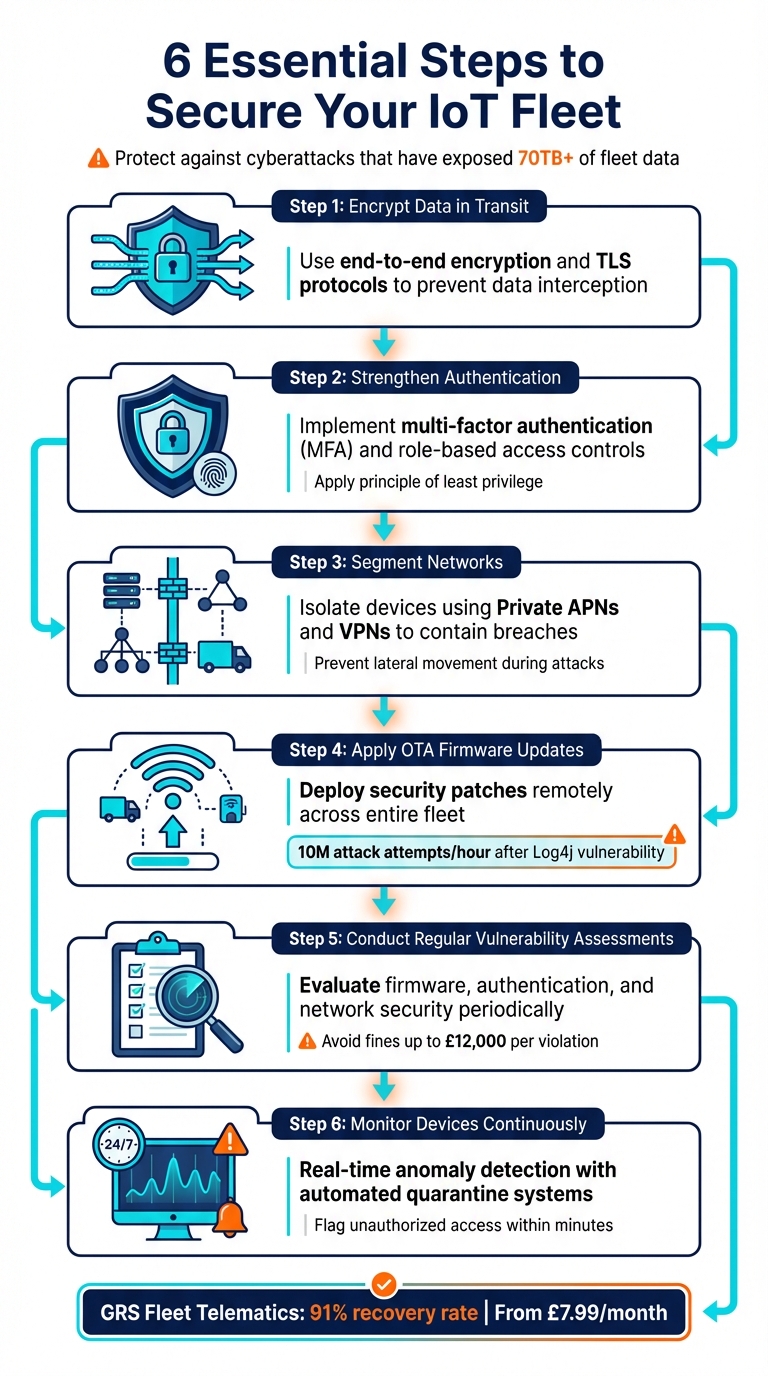
To secure your fleet:
- Encrypt data in transit to prevent interception.
- Strengthen authentication with multi-factor methods and role-based access.
- Segment networks to isolate breaches and limit damage.
- Apply OTA firmware updates to address vulnerabilities quickly.
- Conduct regular vulnerability assessments and prioritise high-risk areas.
- Monitor devices continuously for anomalies and threats.
Solutions like GRS Fleet Telematics offer dual-tracker technology, remote immobilisation, and 24/7 recovery support, ensuring quick response to threats. Starting at £7.99/month, these tools help protect fleets while maintaining compliance and efficiency.
The stakes are high, but by implementing these measures, you can reduce risks, safeguard operations, and comply with regulations.
6 Essential Steps to Secure IoT Fleet Devices from Cyber Threats
IoT Security Best Practices: The Ultimate Guide for 2025
IoT Device Vulnerabilities in Fleet Operations
Fleet IoT devices come with certain vulnerabilities that attackers often exploit. Recognising these weaknesses is the first step towards building effective threat detection and monitoring systems for your fleet. Below, we delve into three key areas where fleets are particularly at risk.
Unencrypted Data Transmission
When data is transmitted without encryption, fleet communications are left wide open to interference. Hackers can intercept sensitive information, tamper with GPS signals to mislead drivers, or even disable vehicle location tracking altogether. Protecting data in transit is essential to safeguarding operations and preventing these types of breaches.
Weak Authentication Protocols
Weak authentication measures make it easier for unauthorised users to gain access to fleet systems. A study by the UK Department for Science, Innovation and Technology highlights that many enterprise IoT devices operate under the 'root' user with outdated bootloaders, leaving them highly vulnerable. This lack of security can allow attackers to seize control of vehicles, disrupt routes by manipulating GPS data, or extract sensitive business information for competitive gain. Strengthening authentication protocols is a critical step in countering these risks.
Expanding Attack Surface with Fleet Growth
As fleets grow, so does the number of potential entry points for cyberattacks. From cellular communications and vehicle CAN buses to cloud servers, larger fleets offer attackers more opportunities to exploit vulnerabilities. This challenge is amplified for fleets spread over vast geographic areas, where centralised monitoring becomes difficult. Poorly maintained devices, outdated firmware, and misconfigured settings only add to the risk. Ensuring consistent security measures across the fleet is vital to reducing the attack surface and maintaining robust defences.
Solutions for Reducing IoT Device Vulnerabilities
Building on previously identified vulnerabilities, there are several targeted measures to enhance security: encrypting data, improving authentication, and segmenting networks.
Data Encryption and Role-Based Access Controls
Unencrypted data and weak authentication are common issues, but they can be tackled with strong encryption protocols and strict access controls.
For data in transit, end-to-end encryption is essential to prevent interception of sensitive information, such as location or operational data. Using TLS suites for secure handshakes and secure chip components to store cryptographic keys ensures that data remains protected.
Authentication should also go beyond basic passwords. Multi-factor authentication (MFA) must be standard for accessing IoT platforms, dashboards, and mobile apps. Additionally, applying the principle of least privilege ensures users only have access to what their role requires. For instance, dispatch staff don’t need the same access as maintenance teams. As Keystone Technology Consultants highlights:
"If a compromised account can view routes and vehicle location at scale, you have an operational and safety risk, not just an IT issue."
Real-world examples underline the risks. The CDK Global ransomware attack, which exploited a vulnerability in a cellular IoT electronic logging device, led to a £19.5 million ransom payment. With nearly half of fleets across various industries integrating management software with back-office systems, granular admin roles and audit logs are vital for spotting and addressing suspicious activity.
Network Segmentation for Breach Containment
Network segmentation is another critical step to contain breaches and limit lateral movement during attacks.
By segmenting your fleet network, compromised devices can be isolated, preventing the breach from spreading to other devices or core systems. Secure environments can be established using Private Access Point Names (APNs) and Virtual Private Networks (VPNs). These measures ensure that external users cannot infiltrate your network.
Connectivity management platforms add another layer of protection, allowing you to monitor traffic in real time and quickly identify unusual patterns. If interference is detected, specific SIM cards or network segments can be remotely disabled without disrupting the entire fleet. This is especially important given the speed of cyberattacks - some occur within just five minutes of a device connecting to the internet, and vulnerabilities can be exploited within 15 minutes of being disclosed publicly.
Over-the-Air (OTA) Firmware Updates
Firmware vulnerabilities present a persistent risk, as they can survive both system reboots and factory resets. Over-the-air (OTA) updates are a vital tool for deploying urgent patches across fleets without needing physical access. For example, following the discovery of the Log4j vulnerability, attack attempts surged to 10 million per hour.
Secure OTA processes rely on asymmetric cryptography and SHA-256 hashing to ensure updates are untampered during transmission. Techniques like A/B partitioning (or blue-green deployment) download new firmware to a secondary partition while the primary remains operational. If the update fails, the system automatically reverts to the functional version, avoiding device downtime. However, as Witekio warns:
"If an OTA pipeline is compromised, the entire fleet is compromised."
The EU Cyber Resilience Act now requires manufacturers to provide security support throughout a product’s lifespan. This includes delivering critical patches separately from feature updates, ensuring vulnerabilities are addressed promptly. Additional measures, such as implementing hardware root of trust with TPM 2.0 and using monotonic version counters to prevent downgrade attacks, further safeguard fleets against emerging threats.
Vulnerability Management Strategies
Having a structured approach to managing vulnerabilities is key to addressing potential risks before they escalate into larger issues.
Regular Vulnerability Assessments
Periodic assessments play a crucial role in identifying weaknesses in IoT systems. These evaluations cover areas such as firmware, authentication protocols, network security, and physical safeguards, all of which are critical to avoiding operational disruptions.
For instance, automated compliance monitoring can help prevent costly regulatory fines. Violations related to Electronic Logging Devices (ELDs) or emissions standards can result in penalties of up to £12,000 per infraction. By conducting these assessments, organisations can pinpoint vulnerabilities that require immediate attention and ensure compliance with regulatory standards.
Risk Prioritisation Based on Impact
Not all vulnerabilities are created equal, which is why prioritisation is essential. The goal is to ensure that the cost of an attack outweighs the potential gains for an attacker. As highlighted in the IoT Device Security White Paper:
"Security is always a balance between economic cost and benefit, dependent upon the value of assets on the one hand and the cost of security features on the other."
Vulnerabilities should be categorised by their attack vector. For example, high-cost invasive hardware attacks, like micro-probing a chip, are less common compared to lower-cost software or communication-based attacks that exploit code flaws or internet protocols.
Particular attention should be given to devices managing high-value cargo, such as pharmaceuticals or cold-chain goods. These are especially vulnerable to environmental failures or data breaches, which can result in significant financial losses and reputational damage. Moreover, high-impact breaches could lead to fines amounting to tens of thousands of pounds. By focusing on the most critical risks, organisations can allocate resources more effectively.
Continuous Monitoring of IoT Devices
Real-time monitoring is a powerful tool for detecting threats before they can escalate. Advanced systems can flag anomalies like unauthorised SIM card changes, suspicious roaming activity, or unexpected shifts in device location.
Automated quarantine systems add another layer of protection by isolating compromised devices without disrupting the entire fleet. Additionally, adopting a Zero Trust architecture minimises the attack surface by isolating sensitive customer data and preventing lateral movement within the network, further enhancing security with enterprise-grade van tracker systems.
Advanced Fleet Security Solutions
Fleet security has evolved to address complex challenges, especially with the rise of IoT vulnerabilities. Modern solutions go beyond basic protections, incorporating multiple layers such as hardware redundancy, real-time monitoring, and rapid response systems. These measures aim to counter both cyber threats and physical theft effectively. A standout example in this field is GRS Fleet Telematics, which offers a robust suite of security features.
GRS Fleet Telematics: Fleet Security Features
GRS Fleet Telematics tackles the risk of single-point failures with its dual-tracker technology. This system pairs a primary hardwired GPS tracker with a concealed Bluetooth backup. If the main tracker is disabled - whether through tampering or theft - the backup ensures the vehicle's location remains visible. This feature complements earlier strategies for managing vulnerabilities in both data and devices.
Another key feature is remote immobilisation, allowing fleet managers to prevent engine starts directly through web or mobile apps. This capability is particularly useful for addressing risks like compromised credentials or theft attempts. The platform also provides automated alerts for critical incidents, such as battery disconnections, towing without engine start, and geofence breaches. These alerts enable swift action to protect assets. Impressively, GRS Fleet Telematics boasts a 91% vehicle recovery rate, with most recoveries occurring within 24 hours - a vital tool in the UK, where a van is stolen every 8.5 minutes. Pricing begins at £7.99 per month for software, with hardware options ranging from £35 for basic tracking to £99 for the most comprehensive security package, which includes immobilisation.
Secure Device Provisioning and Recovery Support
To enhance security further, trackers are professionally installed in discreet locations, making them harder to detect. Additionally, a 24/7 recovery service works closely with law enforcement, transforming passive monitoring into active asset protection. When combined with tamper alerts and remote control features, this multi-faceted approach provides strong defence against increasingly sophisticated theft methods. Together, these measures significantly bolster fleet resilience, ensuring businesses stay one step ahead of potential threats.
Conclusion
The vulnerabilities discussed earlier highlight the urgency for a multi-layered defence approach. IoT weaknesses, such as data exposure and unauthorised access, pose tangible risks. A stark example is the November 2024 breach of a UK telematics provider, which led to the exposure of over 70TB of sensitive data and disrupted commercial fleet operations. The severity of these threats demands immediate and sustained attention.
Addressing these risks requires strong countermeasures. Key strategies include data encryption, network segmentation, and over-the-air firmware updates. These are supported by continuous monitoring and regular vulnerability assessments, which help identify and neutralise threats before they escalate. Implementing these measures not only strengthens operational resilience but also ensures compliance with GDPR requirements.
Security management isn’t a one-time effort - it’s an ongoing process. As threats evolve and fleets grow, centralised platforms offering remote updates and real-time insights become critical. These tools help reduce downtime, control costs, and maintain strong defences against emerging risks.
To meet these challenges, integrated solutions are gaining traction. For instance, GRS Fleet Telematics combines dual-tracker technology, remote immobilisation, and 24/7 recovery support. This approach has achieved an impressive 91% vehicle recovery rate, with pricing starting at just £7.99 per month. Such solutions go beyond passive monitoring, offering active asset protection that helps businesses stay ahead of sophisticated threats while maintaining operational efficiency.
FAQs
What’s the quickest way to reduce IoT risk across an existing fleet?
To minimise IoT risks swiftly, start with strong real-time data encryption. Techniques like TLS 1.2+ and AES-256 are essential for safeguarding sensitive data, such as vehicle locations and driver information.
Next, ensure robust authentication measures are in place. This includes implementing multi-factor authentication (MFA) and role-based access control (RBAC) to restrict access effectively.
Finally, prioritise regular monitoring and audits, and adhere to UK GDPR standards. These steps help identify vulnerabilities early and maintain a secure environment.
How can we roll out OTA firmware updates safely at scale?
To deploy OTA firmware updates securely and at scale, it's essential to have a strong device lifecycle management plan in place. Begin by encrypting update packages with TLS 1.2+ and AES-256 to protect data during transmission. Implement robust authentication methods, such as multi-factor authentication (MFA) and role-based access control (RBAC), to ensure only authorised users can access the system.
To maintain firmware integrity, use digital signatures for verification. Additionally, conduct regular audits, keep an eye out for unusual activity, and establish reliable rollback procedures. These steps help maintain security and ensure updates are deployed without disrupting operations.
What should we monitor to spot an IoT device compromise early?
To spot a compromised IoT device early, keep an eye on critical warning signs. These include unusual activity, irregular patterns in data transmission, abnormal device behaviour, or sudden spikes in network traffic. Be alert for physical tampering or unexpected events like geofence breaches or unplanned shutdowns.
Make it a habit to review API activity logs, access records, and real-time location data. Using anomaly detection tools and setting up alerts can also play a big role in catching and addressing threats quickly. Staying proactive ensures you’re ready to act when something seems off.
