How to Manage IoT Vendor Risks
Michael Bar
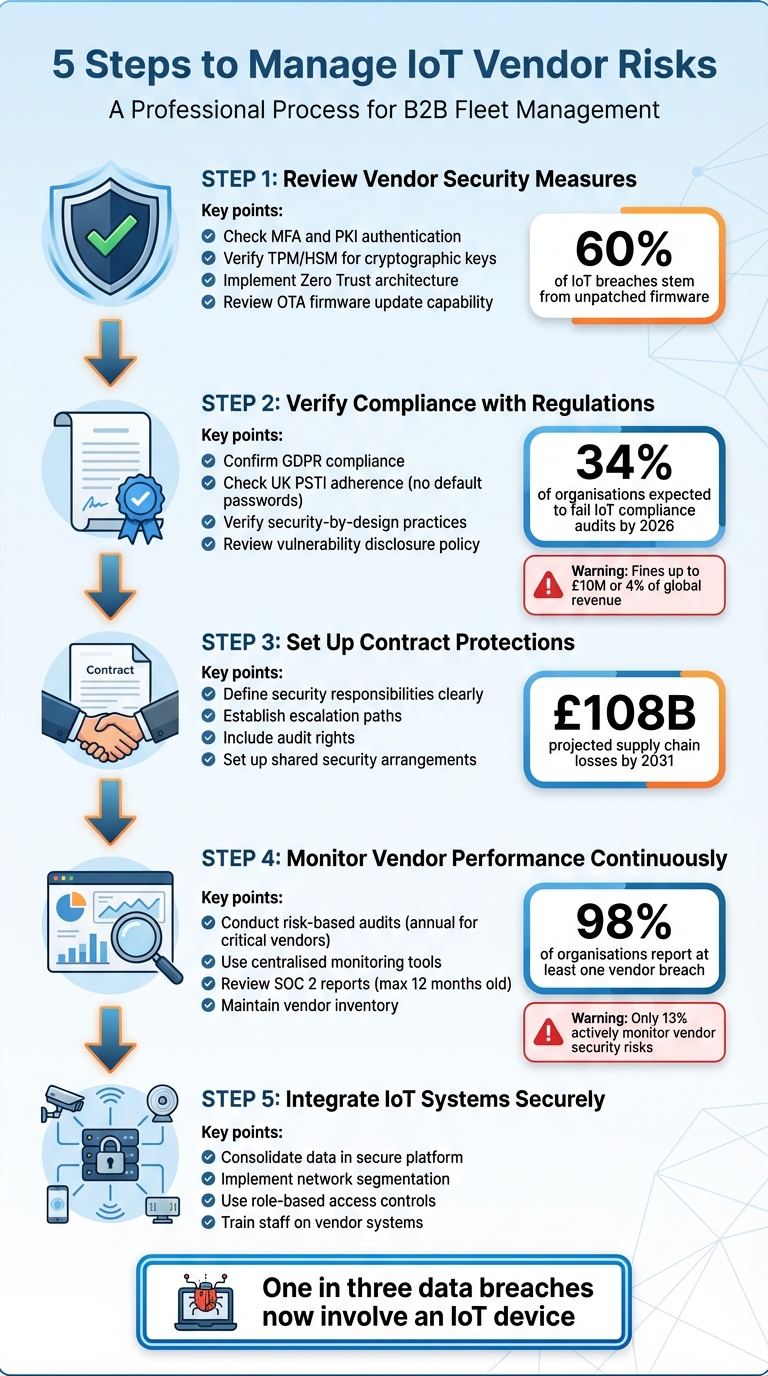
IoT vendor risks can disrupt your operations if not managed properly. These risks arise from vulnerabilities in third-party components like sensors or trackers used in your fleet. Weak security measures, outdated firmware, or non-compliance with regulations can lead to data breaches, downtime, or fines. Here's how to address these challenges:
- Evaluate Vendor Security: Check for strong authentication (e.g., MFA, PKI), secure firmware updates, and incident response plans.
- Ensure Compliance: Verify adherence to GDPR, UK PSTI regulations, and other legal requirements. Look for security-by-design practices.
- Secure Contract Agreements: Define security responsibilities, escalation paths, and shared security protocols in vendor contracts.
- Monitor Vendors Continuously: Conduct regular audits, use monitoring tools, and maintain a centralised vendor inventory.
- Integrate IoT Systems Safely: Use secure platforms, network segmentation, and role-based access controls. Train staff on proper usage.
5-Step IoT Vendor Risk Management Framework for Fleet Operations
Mastering Vendor Management | Cybersecurity Vendor Risk Management Training | TPRM
Step 1: Review Your Vendor's Security Measures
Evaluating your vendor's security framework is essential for safeguarding your fleet. This means digging into their data protection strategies, vulnerability management, and incident response protocols. Each of these elements contributes to the overall resilience and compliance of your fleet operations.
Check Access Controls and Authentication Methods
Strong access controls form the backbone of IoT security. A good starting point is ensuring your vendor implements multi-factor authentication (MFA). As the Information Commissioner's Office (ICO) advises:
"You should implement multifactor authentication wherever it is possible to do so".
MFA adds a critical layer of protection beyond basic passwords, which are notoriously easy to compromise.
Your vendor should also rely on digital certificate-based authentication (PKI) with automated certificate management. This method provides robust cryptographic identity verification and enables mutual authentication, where both the device and the network validate each other.
Additionally, vendors should incorporate Trusted Platform Modules (TPMs) or Hardware Security Modules (HSMs) to store cryptographic keys securely. With the UK PSTI Regulations 2024 now in effect, default passwords are banned, and every device must use unique or user-defined passwords.
Adopting a Zero Trust architecture is another key practice. This model operates on the principle of "never trust, always verify":
"Zero trust principles assume that no device should be trusted by default, regardless of its location or previous authentication status".
This approach ensures that devices in your fleet continuously authenticate and only access specific, authorised resources through micro-segmentation.
Once access controls are reviewed, it's time to focus on how the vendor handles firmware updates and vulnerabilities.
Review Firmware Updates and Vulnerability Handling
Firmware vulnerabilities represent a major security risk. Shockingly, 60% of IoT security breaches stem from unpatched firmware. This makes regular updates an absolute necessity. Vendors should support over-the-air (OTA) updates via BLE, Wi-Fi, or cellular networks. Using a dual-bank firmware architecture ensures updates are verified and fail-safe, avoiding disruptions. Relying on manual updates is not scalable for fleet operations and leaves room for potential security lapses.
"One bad firmware update can turn your entire IoT fleet into expensive paperweights".
Ask your vendor about their staged rollout plan. Updates should initially be deployed to a small test group (5-10% of devices) before rolling out fleet-wide. They should also use cryptographic signing to verify the authenticity of updates and include anti-rollback protection to block attackers from downgrading firmware to vulnerable versions. A cloud-based dashboard for monitoring update success rates and receiving alerts for failed deployments is another must-have.
Examine Incident Response Procedures
Even with the best security measures, incidents can happen. The key is how your vendor handles them. Vendors should have a clear, documented incident response plan with defined escalation paths and response times. Look for a publicly available vulnerability disclosure policy that includes contact details for reporting security issues.
Real-time monitoring and automated threat detection are essential. Many vendors now use AI-driven authentication systems to analyse device behaviour and flag anomalies that could indicate compromised credentials. Compliance with recognised standards such as FIPS 140-3 or ISO 27001 is another indicator of a vendor’s commitment to robust security practices.
With one in three data breaches now involving an IoT device, a thorough evaluation of your vendor's security measures is non-negotiable. This diligence ensures that your fleet remains protected from potential vulnerabilities and operational disruptions.
Step 2: Verify Compliance with Regulations
Once you've reviewed your security measures, the next step is to ensure legal compliance. Staying compliant not only safeguards your fleet data but also helps you avoid hefty penalties. By 2026, 34% of organisations are expected to fail IoT compliance audits, which underscores how important this step is.
Confirm GDPR and Data Privacy Compliance
Your vendor must establish a lawful basis for processing data, such as consent, contractual necessity, or legitimate interests. They should clearly outline who they are, what data they collect, why they need it, who they share it with, and how users can withdraw consent.
Pay close attention to how consent is obtained. Consent should be freely given, specific, informed, and unambiguous. For example, vendors should use opt-in mechanisms instead of pre-ticked boxes or coercive tactics like "confirmshaming". If the IoT devices lack screens or have limited display capabilities, privacy information and consent options should be accessible through a mobile or web app. This ensures compliance across varying legal requirements in the UK.
For IoT devices handling sensitive data - such as biometric, health, or children's information - the vendor must meet stricter "explicit consent" requirements under Article 9 of UK GDPR.
Non-compliance with the UK PSTI regulations can result in fines as high as £10 million or 4% of global revenue.
The next step is to check whether security has been integrated into the device from the beginning.
Check for Security-by-Design Practices
Security-by-design ensures that devices come with built-in protection rather than it being added later. The Product Security and Telecommunications Infrastructure (PSTI) Regulations 2024 require vendors to adhere to key security measures, including:
- No universal default passwords (each device must have a unique password or prompt users to set one).
- A publicly available vulnerability disclosure policy with clear contact details.
- A stated minimum period for security updates.
Before purchasing, confirm the vendor’s "end-of-support" date to ensure the device stays secure for its entire intended lifespan.
Look for compliance with recognised standards like ETSI EN 303 645, ISO 27400:2022, or the NIST IoT cybersecurity baseline. These frameworks guide best practices for cryptography, secure algorithms, and device authentication.
Some vendors also use Privacy-Enhancing Technologies (PETs), such as Trusted Execution Environments (TEE), homomorphic encryption, or differential privacy. These methods minimise data exposure while maintaining functionality. Additionally, data deletion features should allow for easy removal of personal information throughout the product's lifecycle.
By adopting a security-by-design approach, you can reduce risks like operational downtime with van tracking solutions for fleet management.
Finally, make sure the vendor has a robust process for handling vulnerabilities.
Review Vulnerability Notification Processes
A vendor’s vulnerability disclosure policy (VDP) should include a clear reporting channel, a timeline for acknowledging reports, a remediation plan, and a "Safe Harbor" clause. Alarmingly, 41% of manufacturers currently lack a vulnerability disclosure programme.
For critical vulnerabilities, check that the vendor’s policy enforces patching within a specific timeframe - typically 30 days for critical issues and 90 days for high-risk vulnerabilities. The EU Cyber Resilience Act requires vendors to notify authorities of exploited vulnerabilities within 24 hours and disclose patches publicly within 72 hours.
Ask for the vendor’s Software Bill of Materials (SBOM). This document confirms they’re monitoring vulnerabilities in third-party components and libraries, not just their own code. With 29% of IoT vendors lacking secure update processes, ensure the vendor supports automatic over-the-air updates or provides a straightforward manual update process if automation isn’t feasible.
| Regulation | Vulnerability Notification Requirement | Security Update Requirement |
|---|---|---|
| UK PSTI Act | Public contact point; published VDP | Must publish a minimum support period |
| EU Cyber Resilience Act | 24-hour notification for exploited vulnerabilities; 72-hour public disclosure | Minimum 5 years of free security updates |
| US IoT Cybersecurity Act | Accept/respond to reports; 90-day patch for critical issues | Mandatory firmware update capability |
Step 3: Set Up Contract Protections
Once compliance is verified, the next step is to establish solid contractual safeguards. With 75% of software supply chains targeted by attacks in 2024 and projected losses expected to reach £108 billion by 2031, having strong contract protections in place is essential. These agreements lay the groundwork for clear accountability between you and your vendor.
Clarify Security Responsibilities
Your contract should clearly define the security responsibilities of both parties. For example, suppliers are typically responsible for ensuring hardware durability, software performance, continuous data transmission, and implementing measures to safeguard data and comply with privacy laws. Meanwhile, your team would usually handle user authentication protocols and access control measures. Contracts should also enforce the 'least privilege' principle, mandate duty segregation, and require suppliers to map their supply chains to ensure security obligations extend to subcontractors.
Include provisions for audit and remediation rights. This allows you to conduct security reviews, request critical information, and ensure vendors address any security gaps within specified timeframes. For highly sensitive operations, set minimum vetting standards for vendor personnel, such as BPSS, and include indemnification clauses to protect your business against claims from product malfunctions, security breaches, or intellectual property issues. While financial liabilities are often capped, exceptions should be made for gross negligence, intellectual property violations, or breaches of confidentiality.
"Clearly defining the responsibilities of each party within the contract ensures that accountability is established from the start." - Anna Levitina, Author, Logan & Partners
Additionally, your contract should outline escalation procedures to resolve issues quickly.
Define Escalation Paths for Problems
Your agreement should specify formal governance structures, regular reporting schedules, and designated contact points. It’s important to set clear expectations and timelines for how vendors must detect, respond to, and report security incidents. Avoid vague terms like "good industry practice" by referencing established frameworks such as ISO 27001, NIST, or the Cyber Assessment Framework. Broaden the definition of security incidents to include "near misses", encouraging proactive threat management before a breach occurs. Prohibit the use of unsupported software and require vendors to apply timely security patches. Involving legal teams early in the procurement process ensures escalation procedures are both practical and aligned with vendor operations.
"Cyber resilience should be considered from the outset, not added in once terms are agreed." - Jocelyn S Paulley, Partner, Gowling WLG
Consider Shared Security Arrangements
Shared security models can be particularly effective in environments where cloud and IoT systems are integrated. These models clearly outline both legal governance and operational responsibilities. To ensure alignment, map various security frameworks against each other and require vendors to follow your documented data processing instructions. Include protocols for data return or deletion upon contract termination to minimise residual risks. These shared arrangements work hand-in-hand with ongoing vendor monitoring, as discussed in earlier steps.
"Treat suppliers as strategic partners in cyber defence, not just vendors." - Gowling WLG
Finally, assess your organisation's risk appetite before drafting contracts. This will guide the complexity of your templates and the level of scrutiny applied to vendor relationships.
Step 4: Monitor Vendor Performance Continuously
After finalising contracts and ensuring compliance, it’s vital to keep a close eye on vendor performance to maintain fleet security across various industries. Strong contracts are just the beginning; ongoing monitoring ensures vendors stay on track. With 98% of organisations reporting at least one vendor breach and 62% of data breaches linked to third-party vulnerabilities, this step is critical. However, only 13% of organisations actively monitor the security risks posed by their vendors, leaving many fleets exposed to potential threats.
Conduct Regular Vendor Audits
The level of scrutiny a vendor requires should match the risk they pose. Start by categorising IoT suppliers based on the sensitivity of the data they handle and their importance to operations. For example:
- Audit critical vendors annually.
- Review important vendors every two years.
- Assess standard vendors every two to three years.
Check independent audit reports to confirm their security performance. Pay close attention to the "Opinion" section for any qualifications and review the Complementary User Entity Controls (CUECs) to understand the security measures you need to implement for their controls to work effectively. Ensure SOC 2 reports are up-to-date (no older than 12 months) and confirm that the "Description of the System" aligns with the IoT services they’re providing.
Be prepared to reassess vendors immediately if there are significant changes, such as acquisitions, repeated service failures, or a drop in their financial stability.
"Your organisation's security is only as strong as your weakest vendor." - Vision Compliance
After these audits, continuous monitoring can help address any gaps that emerge between formal reviews.
Use Centralised Monitoring Systems
To keep tabs on vendor security between audits, consider using tools like BitSight, SecurityScorecard, or UpGuard. With 60% of companies now managing over 1,000 vendors, according to Gartner, centralised systems make oversight far more manageable.
Automated Governance, Risk, and Compliance (GRC) platforms are particularly helpful. They simplify tasks like distributing questionnaires, collecting evidence, and following up, cutting onboarding times by up to four times and reducing manual risk assessments by as much as 80%.
Keep a centralised inventory of all vendors, detailing their services, data access levels, and current risk scores. Use this inventory to streamline audits and improve transparency. Standardised tools like CAIQ or SIG can provide consistent benchmarks, while converting qualitative audit results into numerical scores allows for easier comparisons and trend tracking.
Work with Vendors on Preventive Maintenance
Beyond monitoring, collaborate with vendors to address potential issues before they escalate. For critical vendors, review SLA reports and incident logs quarterly to spot performance problems early.
When offboarding a vendor, require a written deletion certificate to confirm that all fleet data has been erased from their systems and backups. Regularly review system updates, capacity, and emerging threats to ensure security priorities remain aligned.
Combining proactive maintenance with continuous monitoring helps build a stronger, more secure vendor ecosystem.
Step 5: Integrate IoT Systems Securely
With vendor oversight established, the next step is integrating IoT solutions carefully to avoid creating security vulnerabilities. This process ensures that strong vendor management translates into a secure and efficient fleet operation. Here’s how to centralise IoT data, train your team, and select solutions that protect your fleet effectively.
Consolidate IoT Data in a Secure Platform
Bringing all IoT data together on a single, secure platform simplifies visibility and reduces operational complexity. Middleware can help connect IoT sensors and devices with your existing fleet management or ERP systems, ensuring a seamless flow of information across technologies.
To enhance security, consider network segmentation to keep IoT devices isolated from core business systems. This approach limits potential damage if a vendor’s system is compromised. Additionally, use role-based access controls to ensure staff only access data relevant to their roles. For example, drivers, fleet managers, and administrators should each have tailored permissions. This not only reduces the risk of unauthorised access but also supports compliance with GDPR regulations.
Train Staff on Vendor Systems
Technology alone isn’t enough - your team needs to be equipped with the knowledge to use it securely and effectively. Provide practical, role-specific training to ensure everyone understands their responsibilities. For drivers, focus on how telematics data is collected and used, while fleet managers should gain a deeper understanding of analytics and reporting tools.
Regular training sessions are essential, especially as systems are updated or new security threats emerge. Supplement these with quick-reference guides for troubleshooting and updates, ensuring your team stays informed and confident in using the technology.
Consider Solutions Like GRS Fleet Telematics
When choosing IoT providers, look for solutions that address multiple risks effectively. GRS Fleet Telematics, for instance, offers dual-tracker technology, which ensures continuous vehicle monitoring even if one tracker fails. This feature is particularly useful when dealing with multiple vendor systems, as it ensures operational continuity.
With a 91% recovery rate for stolen vehicles, GRS Fleet Telematics has demonstrated its ability to minimise losses from theft or unauthorised use. Starting from just £7.99 per month, it provides an affordable yet robust tracking solution, making it accessible for organisations of all sizes. By consolidating tracking with a trusted UK-based provider, you can simplify vendor management while maintaining high security standards.
Conclusion
Managing IoT vendor risks requires a blend of strong security practices, strict regulatory adherence, and careful integration strategies. Key steps include evaluating vendor security protocols, ensuring GDPR compliance, setting up clear contractual agreements, and maintaining ongoing performance monitoring. As ENISA aptly states, "IoT security needs to be considered at all stages of the supply chain, from early conceptual design to end-user delivery".
Recognising the complexity of IoT supply chains is equally important. Their intricate nature makes choosing dependable vendors critical to ensuring the safety and efficiency of fleet operations.
Vendors that prioritise security-by-design integrate protective measures from the outset, reducing protocol mismatches and enabling quicker responses to incidents.
Collaborating with UK-based providers like GRS Fleet Telematics simplifies vendor management while maintaining high security standards. Their advanced dual-tracker technology, impressive 91% recovery rate for stolen vehicles, and affordable subscription plans starting at £7.99 per month offer a solid combination of security and fleet management efficiency.
FAQs
What should I ask an IoT vendor before buying?
When you're assessing an IoT vendor, it's important to dig into their security measures, compliance with UK regulations, and data protection strategies. Focus on areas like encryption, role-based access control, and whether they conduct regular security testing. Also, check if they align with UK GDPR requirements.
Don't forget to review their service level agreements (SLAs), particularly regarding system uptime. Ask if they use secure APIs, which are crucial for avoiding data breaches or issues like vehicle theft. These steps help ensure the solution is both secure and dependable.
Which UK regulations matter most for fleet IoT devices?
Fleet IoT devices in the UK must comply with several important regulations to ensure data is handled securely and responsibly. Two key laws to keep in mind are the UK GDPR and the Data (Use and Access) Act. These laws emphasise the need for secure processing of personal data, transparency in how data is used, and implementing safeguards like encryption and access controls.
To meet these requirements, businesses must also carry out Data Protection Impact Assessments (DPIAs) when processing activities are deemed high-risk. DPIAs help identify potential risks to personal data and outline measures to address them.
Additionally, following recognised standards like ISO 27001 for information security management and adhering to the Privacy and Electronic Communications Regulations (PECR) are crucial for lawful operation and maintaining robust data security. These standards and regulations work together to ensure both compliance and the protection of sensitive information.
How do I monitor IoT vendors without constant audits?
To keep an eye on IoT vendors without relying on constant audits, focus on continuous security measures and automated risk management tools. Here’s how:
- Use secure APIs to ensure safe communication between devices.
- Set up real-time alerts to flag any unusual or suspicious activity immediately.
- Conduct regular vulnerability assessments to identify and address potential weaknesses.
Additionally, maintain a comprehensive inventory of all IoT devices in use. Make sure vendors stick to essential security protocols, such as:
- Encrypting data to protect sensitive information.
- Implementing role-based access to limit permissions.
- Using secure authentication methods to prevent unauthorised access.
These steps minimise the need for manual audits while staying ahead of potential risks.
